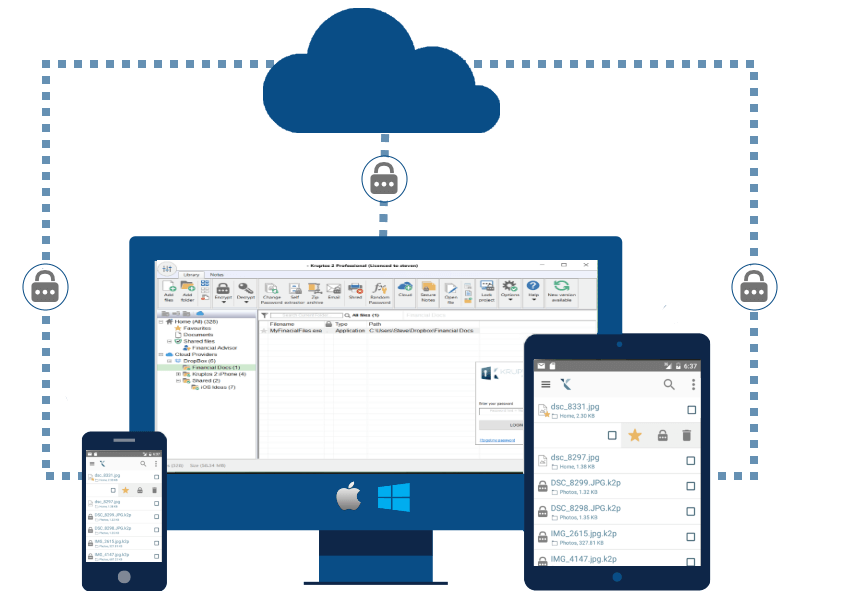
How to Permanently Delete Files Using Kruptos
When you delete a file from your computer, it doesn’t simply disappear from existence—at least, not right away. Even if you immediately empty the Recycle Bin or Trash folder, all your deletion does is earmark the space that file takes up on your hard drive as vacant. Until another file or application comes along to …